Discover Your Complete
Application Attack Surface From Source Code
Map every API and application directly from source code to automatically turn visibility into testing coverage.
The Challenge
You Can’t Secure What You Can’t See
Without clear visibility into your application attack surface, risk assessment becomes educated guesswork. If you don’t know what exists—or what changed—how can you be confident you’re testing the right things?
Code Ships Faster Than Security Can Track
AI-assisted development means new APIs, services, and endpoints appear constantly. Manual inventories fall behind the moment they’re written.
Discovering APIs in Production Is Too Late
Traditional discovery tools wait for network traffic—finding APIs after deployment. That’s visibility after exposure, not before risk.
Modern Application Components Introduce New Risks
Microservices, serverless functions, and AI/LLM integrations quietly multiply your attack surface—far beyond what legacy inventories were built to track.
How it Works
Source Code Visibility is the Secret
to AppSec Testing That Scales
Continuous Source Code Visibility
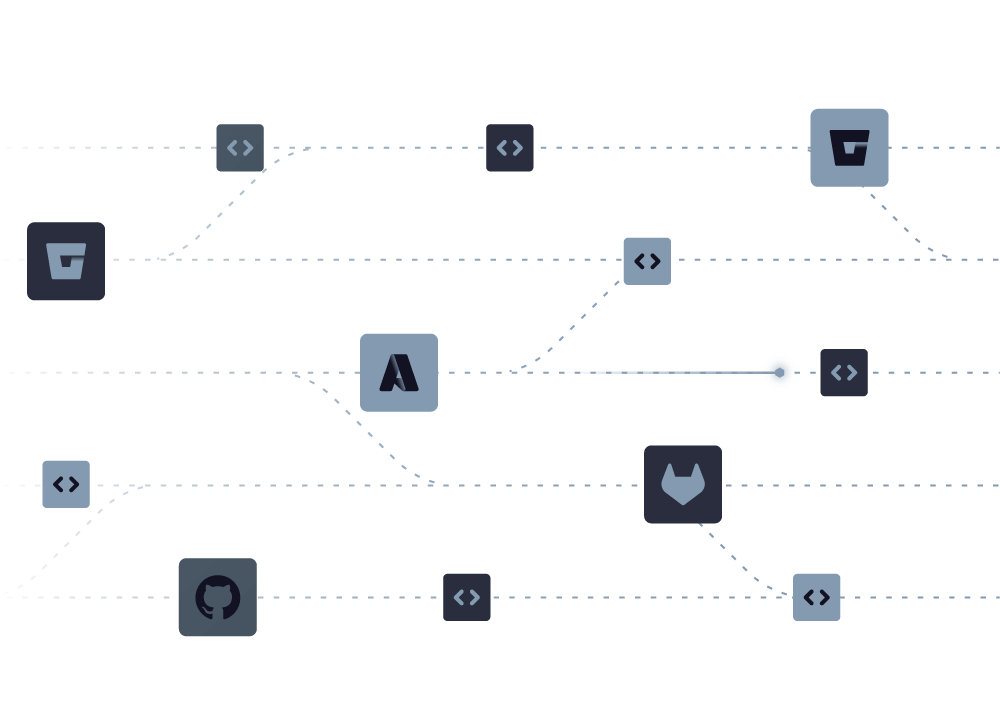
- Connects directly to GitHub, GitLab, or Bitbucket—no agents, no production scanning
- Analyzes every repository to identify APIs, applications, and testable attack surface
- Detects REST, GraphQL, gRPC, WebSocket endpoints, and serverless functions
- Updates continuously with every commit—your inventory never gets stale
Surface App Risk Insights Directly from Repositories
- Identifies which applications handle sensitive data (PII, PCI, HIPAA) at the code level
- Surfaces commit activity and change velocity to flag fast-moving, high-risk repos
- Distinguishes testable applications from documentation repos, libraries, and infra
- Helps small AppSec teams focus on the 15 apps that matter, not the 100 that exist
From Discovery to Testing—Automatically
- Auto-generates OpenAPI specifications directly from code using AI
- Eliminates manual spec writing and maintenance overhead
- Specs update continuously as code changes—no more outdated documentation
- Bridges the gap between discovered API to configured DAST scan
StackHawk Uncovers What Matters Most
Get complete visibility into your application attack surface, from API types and sensitive data to the languages and frameworks in use across your repositories.
APIs
REST, GraphQL, gRPC, WebSocket endpoints
App Components
Microservices, serverless functions, and more
Sensitive Data
Languages & Frameworks
See it in Action
Discover Your Complete
API Attack Surface from Source Code
API Discovery
StackHawk integrates with your source code repositories to map all your apps and APIs, giving you complete visibility across your attack surface.
Repo Insights
To help prioritize which apps and APIs to test, StackHawk automatically identifies where sensitive data lives, languages and frameworks in use, and commit activity.
OpenAPI Spec Generation
What Visibility Looks Like in Practice
Eliminate Shadow APIs
Discover every endpoint before it reaches production—no more pen test surprises, no unknown exposure.
Prioritize with Confidence
Understand which apps handle sensitive data and change frequently—focus effort where real risk lives.
Accelerate Time to Test
Auto-generated OpenAPI specs turn discovery directly into testing coverage, without configuration bottlenecks.
Go Beyond Application Attack Surface Discovery
Test What You Discover
Visibility without testing is just an inventory. See how StackHawk’s runtime testing validates your attack surface.
Get Complete AppSec Intelligence
Discovery, testing, and oversight working together. Know what exists, test what matters, prove it’s working.